Secure Password Plugins for libPurple
 One of the security issues with libPurple (the engine behind Pidgin
and many other IM programs) is that it stores passwords as plain text.
The developers have chosen to do this because simple methods of
encrypting passwords would be easily exploited, causing a false sense
of security. These plugins encrypt libPurple passwords using third-party password and credential management programs.
One of the security issues with libPurple (the engine behind Pidgin
and many other IM programs) is that it stores passwords as plain text.
The developers have chosen to do this because simple methods of
encrypting passwords would be easily exploited, causing a false sense
of security. These plugins encrypt libPurple passwords using third-party password and credential management programs.
Usage Instructions
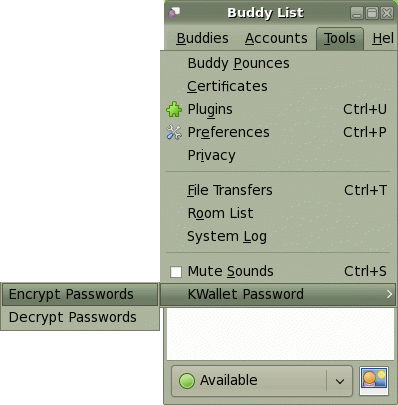
After installing the plugin of your choice, you must enable the plugin.
In Pidgin, plugins are found under Tools.
You must place a check in the box next to the plugin that you have installed.
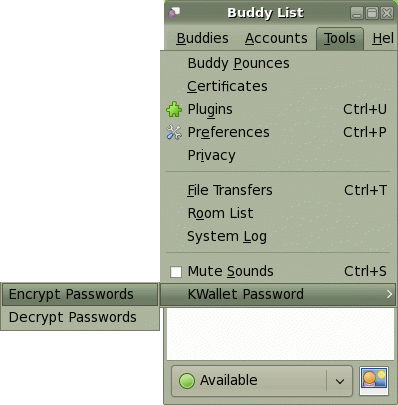 When the plugin is installed and enabled, a new menu item will be available under tools.
It contains two options:
When the plugin is installed and enabled, a new menu item will be available under tools.
It contains two options:
- Encrypt Passwords
-
This will locate all passwords that are currently stored as plain text
in your accounts file. Each password will be stored securely in the
password/credentials management service handled by the plugin. Once
secured, the plain text password will be removed from your accounts
file. From this point on, all passwords are stored securely and will be
automatically loaded when you start Pidgin (or the program that uses libPurple).
- Decrypt Passwords
-
There are multiple reasons for wanting to have your passwords stored as
plain text after using this plugin. For example, You may want to copy
your accounts file to another program. You may want to switch to a
different password securing plugin. You may just want to start using
plain text passwords again. This function will remove all passwords
from the password/credentials management service and restore them as
plain text in your accounts file. You must run Encrypt Passwords again
if you want to resecure your passwords.
Plugin Versions
This plugin comes in multiple versions to make use of as many popular password/credential management services as possible.
Currently, the following versions are available:
-
 KWallet
KWallet
-
The KWallet
plugin saves passwords in KDE's KWallet credential management service.
A binary is available, built with KDE 3.5 and Pidgin 2.3. Simply
download the so file to ~/.purple/plugins/ (you may need to
create this folder). If the binary does not work, download and compile
the source code according to the instructions at the top of the file.
-
 Windows
Windows
-
The Windows plugin encrypts passwords using Windows CryptoAPI. A binary
is available, built for Windows XP. Copy the dll file to C:\Program Files\Pidgin\plugins\. A source file is available also. See the readme file for notes on compiling the source file.
The structure of these plugins is a very good starting point for
developing more plugins. If you are a programmer and you would like to
implement this plugin with a different password/credentials management
service, please feel free to do so. Once finished, we will be happy to
host your plugin here with the other secure password plugins.
Files
| File |
Version |
Date |
|
| KWallet Password Plugin (binary) |
1.0 |
2008-04-30 |
Download |
| KWallet Password Plugin (source) |
1.0 |
2008-05-08 |
Download |
| KWallet Password Plugin (readme) |
1.0 |
2008-05-08 |
View |
| Windows Password Plugin (binary) |
1.0 |
2008-05-08 |
Download |
| Windows Password Plugin (source) |
1.0 |
2008-05-08 |
Download |
| Windows Password Plugin (readme) |
1.0 |
2008-05-08 |
View |
Suggested Projects
One of the goals of creating the KDE and Windows plugins was to
demonstrate how easily similar plugins could be created. The following
are suggested projects that should be easy to develop with slight
alterations to the existing KDE or Windows code.
- KDE4 D-BUS
-
This has been developed and is available
here.
- KeePass
- From
Haudy Kazemi: KeePass is a Windows password manager that supports USB
removable media. This may be used to provide secure password storage
for Pidgin Portable.
- Gnome Keyring
- Many people
have asked for the KDE version of this plugin to be compiled for Gnome
Keyring. Doing so should be trivial. First, remove all the KDE-specific
code required to make GTK+ and Qt work together. Then, replace the call
to KDE Wallet's save and get functions with Gnome Keyring's save and
get functions. None of the developers currently on this project have
Gnome, so this conversion has not been attempted.
Contact
This is an open-source project. If you have changes to submit to this
code or if you have a plugin that uses a different password/credentials
management service, please let us know by sending an email to cs@kainaw.com.
History
This began is a class project at the Missouri University of Science and Technology. The resulting paper from the project is available here.
 One of the security issues with libPurple (the engine behind Pidgin
and many other IM programs) is that it stores passwords as plain text.
The developers have chosen to do this because simple methods of
encrypting passwords would be easily exploited, causing a false sense
of security. These plugins encrypt libPurple passwords using third-party password and credential management programs.
One of the security issues with libPurple (the engine behind Pidgin
and many other IM programs) is that it stores passwords as plain text.
The developers have chosen to do this because simple methods of
encrypting passwords would be easily exploited, causing a false sense
of security. These plugins encrypt libPurple passwords using third-party password and credential management programs.
 When the plugin is installed and enabled, a new menu item will be available under tools.
It contains two options:
When the plugin is installed and enabled, a new menu item will be available under tools.
It contains two options:
 KWallet
KWallet
 Windows
Windows